Is Shift-Left Testing in DevSecOps the Key to Early Defect Detection?

Quick Summary:
Shift-Left Testing in DevSecOps is rapidly gaining traction among modern software teams. It promises faster release cycles, fewer security flaws, and greater control over code quality by identifying issues early in the development lifecycle. This blog explores its importance, technical benefits, implementation strategies, and how ImpactQA enables secure, early testing tailored for DevSecOps and SAP environments.
Table of Contents:
- Introduction
- Understanding Shift-Left Testing in DevSecOps
- Benefits of Early Testing and Security Integration
- Implementing Shift-Left Testing: Strategies and Best Practices
- Challenges in Adopting Shift-Left Testing
- Shift-Left Testing and Security Automation
- Building a Culture of Early Testing
- How ImpactQA Enables Shift-Left Testing in DevSecOps
What if you could catch 70% of critical defects before your first code review? That’s the goal of integrating testing earlier in the development cycle. The shift-left approach is not new, but it is redefining software assurance in the context of DevSecOps.
Traditional testing happens late in the SDLC – often right before release. This delay results in cost overruns, slower feedback loops, and higher security risks. According to IBM, fixing a bug found in production can cost 100x more than one identified during the design phase.
Shift-Left Testing in DevSecOps ensures that testing, especially security and functional validation, begins alongside development. This approach shortens feedback loops and identifies defects and vulnerabilities before they become expensive problems. It saves effort, reduces risk, and maintains high release velocity.
Understanding Shift-Left Testing in DevSecOps
Shift-left testing involves pushing QA and security checks to the left of the development timeline. Instead of validating software after development is complete, teams run tests in parallel with coding.
In DevSecOps, this philosophy gets an upgrade. Security testing is embedded directly into CI/CD pipelines. DevSecOps encourages developers, testers, and security professionals to collaborate from the very beginning.
Key components include:
- Static Application Security Testing (SAST) early in the code pipeline
- Unit and API tests integrated with build processes
- Security gates are enforced at each commit
The goal is to transform testing into a continuous, proactive activity rather than a reactive checkpoint.
Benefits of Early Testing and Security Integration
Why wait until the final stages to find issues that could have been avoided much earlier? By integrating testing and security from the start, DevSecOps teams create a development rhythm that values precision over patchwork.
1. Faster Defect Detection
Feedback loops begin early. Developers identify bugs at the code level itself. Fixes are quick and do not compound into major issues later.
2. Reduced Cost of Fixes
Defects caught in the initial stages cost far less than those found in staging or production. Security flaws are flagged before they’re embedded into workflows. This avoids rework and downtime.
3. Better Code Quality
Every code commit passes through functional and security checks. This prevents regressions and helps maintain a clean, tested codebase.
4. Lower Business and Security Risk
Teams catch vulnerabilities before they escalate. This reduces the risk of breaches, financial losses, and non-compliance with regulations.
5. Accelerated Development Cycles
Testing and validation are continuous. There are no long pauses waiting for QA handoffs. This helps teams deliver features faster with fewer rollback incidents.
6. Stronger Cross-Functional Collaboration
Developers, testers, and security analysts work together from the beginning. This shared responsibility breaks silos. Everyone contributes to quality and security, not just a single team.
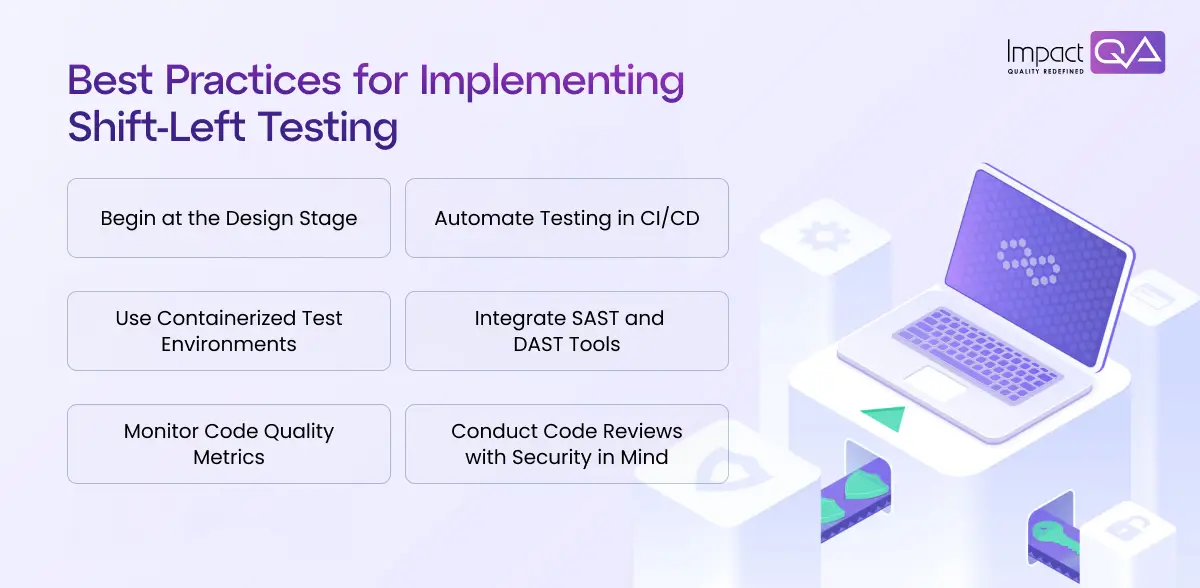
Implementing Shift-Left Testing: Strategies and Best Practices
Shifting left is not just about moving tasks earlier. It involves changing how teams think, plan, and build software. A reactive mindset must give way to a proactive approach. Every step, from design to deployment, must include testing and security. Here’s how to implement shift-left testing in DevSecOps workflows effectively:
1. Begin at the Design Stage
Start security analysis before the first line of code. Use threat modeling to identify risks during design. Apply static code analysis tools to architecture documents and early prototypes.
2. Automate Testing in CI/CD
Automation is essential. Every code commit should trigger unit, integration, and security tests. Set up pipelines to fail fast if quality gates aren’t met. Use test coordination to manage dependencies and parallel execution.
3. Use Containerized Test Environments
Test environments should match production as closely as possible. Use Docker or Kubernetes to spin up lightweight, isolated environments. Ensure they are reproducible and support fast scaling.
4. Integrate SAST and DAST Tools
Embed security tools into your building process. Static Application Security Testing (SAST) tools catch issues in code, while dynamic Application Security Testing (DAST) tools catch issues during runtime. Automate both for continuous insights.
5. Monitor Code Quality Metrics
Define code quality gates in your CI pipeline. Use metrics like code coverage, cyclomatic complexity, and test execution time. Enforce them strictly. Block mergers that don’t meet quality thresholds.
6. Conduct Code Reviews with Security in Mind
Update review checklists to include security validations. Reviewers should look for unsafe functions, missing input validation, and permission issues. Train engineers to spot patterns that lead to vulnerabilities.
This approach requires clear communication and consistent enforcement. But the benefits – faster detection, fewer bugs, better code – make the effort worthwhile. Each of these practices works together to shift defect detection left, building software that’s stable, secure, and scalable from day one.
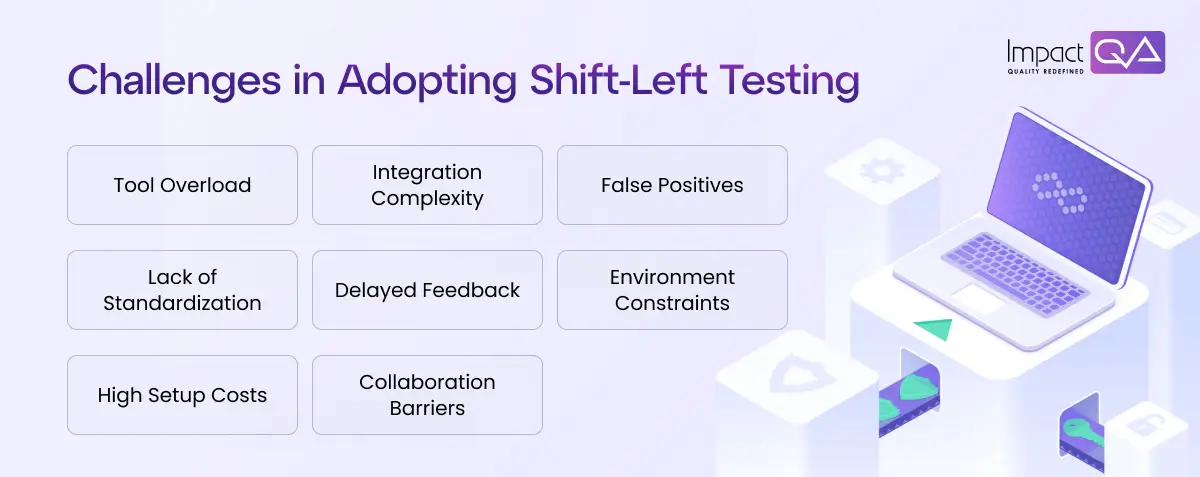
Challenges in Adopting Shift-Left Testing
Shifting left brings clear advantages. But the transition is not without hurdles. The shift often disrupts established routines and introduces new responsibilities. These challenges can delay adoption or reduce impact if not addressed early.
1. Tool Overload
Teams often deal with multiple tools for testing. Functional, performance, and security tools must work together. Managing them increases complexity and overhead.
2. Integration Complexity
Legacy systems pose real barriers. Older monolithic applications are hard to integrate with modern toolchains. Pipelines become unstable or fragmented.
3. False Positives
Automated scans can flag too many non-issues. This leads to alert fatigue. Important issues may get missed or ignored.
4. Lack of Standardization
Without defined testing standards, practices vary widely across teams. Results become inconsistent. Quality and security benchmarks are difficult to enforce.
5. Delayed Feedback
Improper pipeline setups can delay results. Long-running tests slow down development. Developers lose trust in automation.
6. Environment Constraints
Inconsistent or unstable test environments affect test reliability. Local setups differ from staging or production. Bugs slip through undetected.
7. High Setup Costs
Initial setup demands time and budget. Tool licensing, pipeline engineering, and training increase early investment. ROI takes time to show.
8. Collaboration Barriers
Security and development teams often work in silos. Without clear communication, responsibilities blur. Issues remain unresolved or are discovered too late.
Shift-Left Testing and Security Automation
Security automation amplifies the value of shift-left testing. By embedding security tools directly into CI/CD workflows, organizations remove dependency on manual checks.
Key practices include:
- Automated SAST scans on every code commit
- Container image scans for vulnerabilities
- Secrets detection and code signing validations
- Security test triggers at merge and deployment events
Security-as-Code is also gaining traction. Teams treat security policies as code artifacts, version-controlled and auditable. This ensures transparency and consistency.
Test coordination platforms help manage dependencies and automate the execution of unit, functional, and security test cases.
The result? Better risk visibility and faster issue resolution without slowing development velocity.
Building a Culture of Early Testing
Every successful shift-left strategy depends on tools and automation and how teams think and work. Process changes often fall short when a mindset shift doesn’t support them. Early testing needs to become second nature – a core habit within the development cycle, not a box to check at the end.
A strong culture of early testing starts with a shared sense of responsibility. Developers, testers, and security teams must work toward the same goal – stable, secure, and production-ready code from day one. This requires clarity, training, and consistent support from leadership.
- Encourage Shared Responsibility
Testing is not the QA team’s job alone. Developers should treat unit tests and static code analysis as part of their core responsibilities. Code should not be considered complete unless it’s validated for quality and security.
- Involve QA and Security Early
Quality and security teams must be included in sprint planning and backlog grooming. Their early input helps shape stories and acceptance criteria. When feedback is continuous, rework reduces, and test coverage improves.
- Prioritize Training and Knowledge Sharing
Host regular workshops focused on test automation tools, code review techniques, and security best practices. Teams need time and space to get comfortable with early testing frameworks and scripting standards.
- Measure and Reward Meaningful Metrics
Use metrics like test pass rates, time to detect defects, and escaped bugs to gauge progress. Avoid vanity metrics. Reward teams that deliver clean builds consistently and reduce rework over time.
- Support Experimentation
Allow teams to test new tools, frameworks, and integrations. Small improvements in testing pipelines can make big differences in delivery speed and defect reduction. Celebrate these initiatives.
- Ensure Strong Communication Loops
Testing feedback must flow fast. Whether through dashboards or instant alerts, ensure developers are never waiting on QA. Clear visibility into test results speeds up decision-making.
A culture that values early testing doesn’t form overnight. But when it’s part of everyday behavior, quality stops being a separate task and becomes how work gets done.
How ImpactQA Enables Shift-Left Testing in DevSecOps
Shift-Left Testing in DevSecOps only delivers results when combined with technical depth and domain-specific strategies. ImpactQA empowers engineering teams with both. ImpactQA’s DevSecOps testing services focus on embedding quality and security right from ideation to deployment. We bring deep testing expertise across various industries including BFSI, retail, healthcare, and energy.
What ImpactQA Offers:
- CI/CD Pipeline Integration: ImpactQA integrates unit, functional, and security tests directly into DevOps workflows.
- Automated Security Validation: Their SAP-focused security checks address role-based vulnerabilities and critical configuration risks.
- Custom Frameworks: Based on technologies like Selenium, Appium, JUnit, and OWASP tools, their frameworks are tailored to client ecosystems.
- Centralized Test Management and Reporting: Detailed analytics help decision-makers trace quality trends and respond quickly.
- Developer Enablement: Workshops and continuous support help clients scale in-house capabilities.